Documents
Poster
A FORMAT COMPLIANT ENCRYPTION METHOD FOR 3D OBJECTS ALLOWING HIERARCHICAL DECRYPTION
- Citation Author(s):
- Submitted by:
- William Puech
- Last updated:
- 29 March 2024 - 10:08am
- Document Type:
- Poster
- Document Year:
- 2024
- Event:
- Presenters:
- William PUECH
- Paper Code:
- #11461
- Categories:
- Keywords:
- Log in to post comments
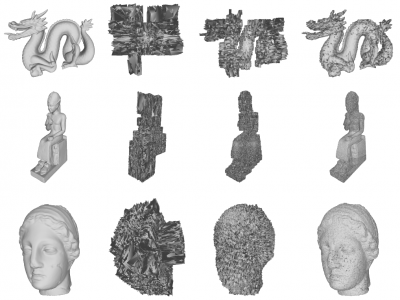
With the increasing popularity of 3D objects in industry and everyday life, 3D object security has become essential. While there exists methods for 3D selective encryption, where a clear 3D object is encrypted so that the result has the desired level of visual security, to our knowledge, no method exists for decrypting encrypted 3D objects hierarchically. In this paper, we are the first to propose propose a method which allows us to hierarchically decrypt an encrypted 3D object according to a generated ring of keys. This ring consists of a set of keys that allow a stronger or weaker decryption of the encrypted 3D object. Each hierarchically decrypted 3D object has a different visual security level, where the 3D object is more or less visually accessible. Based on a master key, these hierarchical keys are generated using our method during the encryption process. Our method is essential when it comes to preventing trade secrets from being leaked from within a company or by exterior attackers. It is also ecologically friendly and more secure than traditional selective encryption methods.


Comments
No comment
No comment