
- Read more about Cryptographic Side-Channel Signaling and Authentication via Fingerprint Embedding
- Log in to post comments
We describe a general framework for designing and embedding a fingerprint at the physical layer of a wireless network to achieve authentication with enhanced security and stealth. Fingerprint embedding is a key-aided process of superimposing a low-power tag to the primary message waveform for the purpose of authenticating the transmission. The tag is uniquely created from the message and key, and successful authentication is achieved when the correct tag is detected by the receiver.
- Categories:
 52 Views
52 Views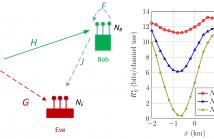
- Read more about A MINORIZATION-MAXIMIZATION (MM) ALGORITHM FOR ARTIFICIAL NOISE (AN)-BASED MIMOME SECRECY RATE MAXIMIZATION
- Log in to post comments
We consider the problem of secrecy rate maximization in a multi-input multi-output multi-eavesdropper (MIMOME) wiretap channel and present an exact solution. A general system model with a multi-antenna eavesdropper and a multi-antenna full-duplex receiver is considered. In particular, we perform joint beamforming and artificial noise optimization in an effort to maximize the achievable secrecy rate. The optimization is performed in the presence of artificial noise generated by both transmitter and legitimate receiver. The resulting optimization problem is non-convex and difficult to solve.
- Categories:
 45 Views
45 Views
- Read more about Robust Energy-Efficient Transmit Design for MISOME Wiretap Channels
- Log in to post comments
This paper considers an energy-efficient transmit design in a general multiple-input single-output multiple-eavesdropper (MISOME) wiretap channel. Specifically, a transmitter sends one confidential message to a legitimate receiver, which must be kept perfectly secure from several external multi-antenna eavesdroppers. Assuming imperfect channel state information (CSI) at the transmitter, our goal is to design the input transmit covariance, such that the worst-case secrecy energy efficiency (WC-SEE) is maximized, subject to the quality of service (QoS) and total transmit power constraints.
- Categories:
 18 Views
18 Views