
- Read more about CNN-BASED DETECTION OF GENERIC CONTRAST ADJUSTMENT WITH JPEG POST-PROCESSING
- Log in to post comments
Detection of contrast adjustments in the presence of JPEG post processing is known to be a challenging task. JPEG post-processing is often applied innocently, as JPEG is the most common image format, or it may correspond to a laundering attack when it is purposely applied to erase the traces of manipulation. In this paper, we propose a CNN-based detector for generic contrast adjustment, which is robust to JPEG compression.
- Categories:
 17 Views
17 Views
- Read more about LEARNED FORENSIC SOURCE SIMILARITY FOR UNKNOWN CAMERA MODELS
- Log in to post comments
Information about an image's source camera model is important knowledge in many forensic investigations. In this paper we propose a system that compares two image patches to determine if they were captured by the same camera model. To do this, we first train a CNN based feature extractor to output generic, high level features which encode information about the source camera model of an image patch. Then, we learn a similarity measure that maps pairs of these features to a score indicating whether the two image patches were captured by the same or different camera models.
main.pdf
- Categories:
 63 Views
63 Views
- Read more about AUGMENTED DATA AND IMPROVED NOISE RESIDUAL-BASED CNN FOR PRINTER SOURCE IDENTIFICATION
- Log in to post comments
- Categories:
 30 Views
30 Views
- Read more about A ROTATION-INVARIANT CONVOLUTIONAL NEURAL NETWORK FOR IMAGE ENHANCEMENT FORENSICS
- Log in to post comments
- Categories:
 62 Views
62 Views- Read more about Median Filtering Forensics Based on Discriminative Multi-Scale Sparse Coding
- Log in to post comments
- Categories:
 13 Views
13 Views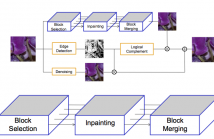
- Read more about INPAINTING-BASED CAMERA ANONYMIZATION
- Log in to post comments
Over the years, the forensic community has developed a series of very accurate camera attribution algorithms enabling to detect which device has been used to acquire an image with outstanding results. Many of these methods are based on photo response non uniformity (PRNU) that allows tracing back a picture to the camera used to shoot it. However, when privacy is required, it would be desirable to anonymize photos, unlinking them from their specific device. This paper investigates a new and alternative approach to image anonymization task.
- Categories:
 26 Views
26 ViewsGiven a query image or video, or a known camera fingerprint, there is a lack of capabilities for fast identification of media, from a large repository of images and videos, that match the query fingerprint.
This work introduces a new approach that improves the computation efficiency of pairwise camera fingerprint matching and incorporates group testing to make the search more effective.
Hybrid.pdf
- Categories:
 15 Views
15 Views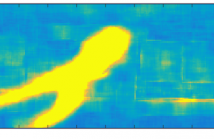
- Categories:
 13 Views
13 Views- Read more about A Consistent Two-Level Metric for Evaluation of Automated Abandoned Object Detection Methods
- Log in to post comments
Scientific interest in automated abandoned object detection algorithms using visual information is high and many related systems have been published in recent years. However, most evaluation techniques rely only on statistical evaluation on the object level.
- Categories:
 23 Views
23 Views- Read more about Copy move forgery detection with similar but genuine objects
- Log in to post comments
Copy-Move Forgery Detection (CMFD) is a well-studied
image forensics problem. However, CMFD with Similar but
Genuine Objects (SGO) has received relatively less attention.
Recently, it has been found that current state-of-the-art
CFMD techniques are mostly inadequate in satisfactorily
solving this important problem variant. In this paper, we have
addressed this issue by using Rotated Local Binary Pattern
(RLBP) based rotation-invariant texture features, followed
by Generalized Two Nearest Neighbourhood (g2NN) based
ICIP_Poster.pdf
- Categories:
 16 Views
16 Views